I was reading about full-disk encryption tools when I came across this five-year old research paper. For me, it was an eye-popper.
Like many, I also assumed that once you power down a computer, the contents of its RAM are scrambled essentially instantaneously. But this is not the case (and it really should not come as a surprise given the way DRAM works). Quite the contrary, a near-perfect image remains in memory for seconds; and if the memory is cooled to extreme low temperatures, the image may be preserved for minutes or hours.
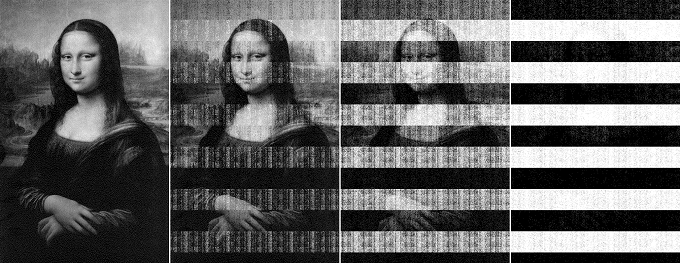
Decay of a bitmap image 5, 30, 60 seconds and 5 minutes after power loss in a 128 MB Infineon memory module manufactured in 1999. From https://citp.princeton.edu/research/memory/.
So even as we worry about public servants losing USB keys or entire laptops containing unencrypted information on hundreds of thousands of people, it appears that sometimes even encryption is not enough. If a lost laptop is in a suspended state, an attacker could access the contents of its RAM using only a rudimentary toolkit (that may include “canned air” dusters turned upside-down for cooling).
I wonder what the future will bring. Tamper-proof hardware in every laptop? In-memory encryption? Or perhaps we will decide that we just don’t care, since we already share most details about our personal lives through social networks anyway?
On that note, Canada’s government just decided to scrap a planned cybersurveillance bill that many found unacceptably intrusive. Good riddance, I say.